How to Bypass CreepJS Browser Fingerprinting

What if browser fingerprinting tools like CreepJS
Browser fingerprinting is basically a way websites collect information about your browser and device to create a kind of digital “profile.” This profile can be surprisingly unique, even without using cookies.
Tools like CreepJS gather details such as your browser and operating system, your time zone and language, the fonts you have installed, any visible extensions, your device type, and your screen size. Since most of these things don’t change very often, fingerprinting can stick with you across different browsing sessions.
In this article, we take a closer look at how CreepJS works, what it’s good at, and where it has limitations. We also walk through how it can be used for testing and research, and mention a few other tools that offer similar insights into how fingerprinting works and how it affects online privacy.
Key points
- How CreepJS examines your browser for inconsistencies or unusual behavior
- How it uses Canvas, WebGL, audio tests, and other signals to map out your device’s unique traits
- How entropy and trust scores help show how identifiable your setup is
- How different browsers, privacy tools, and settings can change what your fingerprint looks like
- Other tools that can help researchers learn more about fingerprinting and blocking systems
What is CreepJS and how does it work?
CreepJS works in a few main steps: it collects data from the browser, processes it, and then analyzes it to build a detailed fingerprint. It pulls info from many APIs, checks how the browser renders graphics, and looks for signs that something is being hidden or spoofed.
- Data Collection - CreepJS gathers lots of signals: window and navigator info, screen details, Canvas and WebGL output, audio context data, fonts, CSS behavior, math quirks, console errors, and more. The goal is to capture enough points to uniquely identify the environment.
- Hashing - All collected data gets hashed into short, fixed strings. This makes fingerprints easier to compare and store.
- Fingerprint Creation - The hashed data is grouped into categories like browser features, screen properties, audio, fonts, rendering, and so on. Together, these form the final fingerprint.
- API Interaction - CreepJS uses internal APIs to analyze the fingerprint, compare patterns, and flag unusual behavior.
- Entropy Analysis - Each component is scored based on how unique it is. Higher entropy means that detail is more identifying.
- Trust Score - CreepJS checks for inconsistencies or modified behavior and then generates a trust score for how "real" the environment looks.
- Resistance Detection - It can detect privacy-focused browsers, extensions, and tools that change or hide fingerprint data.
- Rendering Results - All findings are displayed in a clean UI with charts, stats, and breakdowns of each fingerprint component.
CreepJS Fingerprinting Techniques
CreepJS uses a wide range of advanced methods to build a detailed profile of a browser and device. These techniques are not just theory. They rely on real web technologies and real browser behavior. Here is a quick look at how it works.
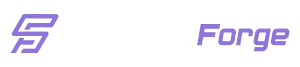
WebGL Fingerprinting
WebGL fingerprinting looks at the small differences in how each device draws 3D graphics. These differences come from the GPU and the graphics drivers, and they can help identify a browser.
In my project, CreepJS, I collect a few key pieces of WebGL info:
- Basic WebGL settings
- GPU vendor and model
- Supported WebGL extensions
- How the device handles certain rendering tasks This helps create a more accurate fingerprint without needing anything invasive.
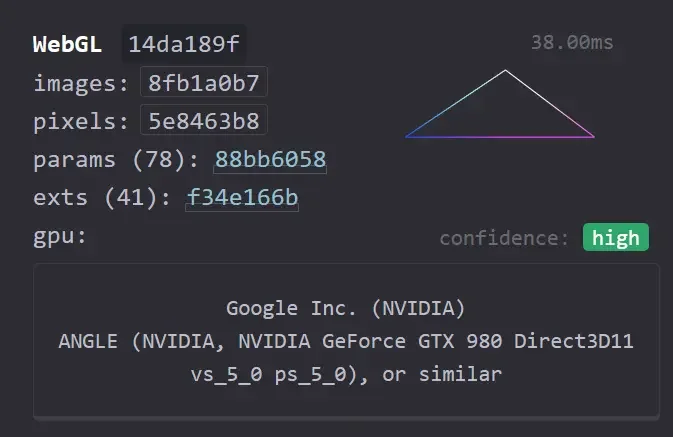
Screen Fingerprinting
Screen fingerprinting looks at the details of a user’s display. In CreepJS, I collect a few basic screen properties:
- Screen resolution
- Color depth
- Pixel depth
- Available screen size
- Device pixel ratio
 These values help build a more reliable fingerprint without needing any personal data.
These values help build a more reliable fingerprint without needing any personal data.
Canvas Fingerprinting
Canvas fingerprinting works by using the HTML5 Canvas to draw images or text and then creating a hash from the final output. Small rendering differences between devices make the result unique.
In CreepJS, I collect several Canvas-related details, including:
- How images are rendered
- Paint and drawing operations
- Text rendering
- Emoji rendering
- Text metrics
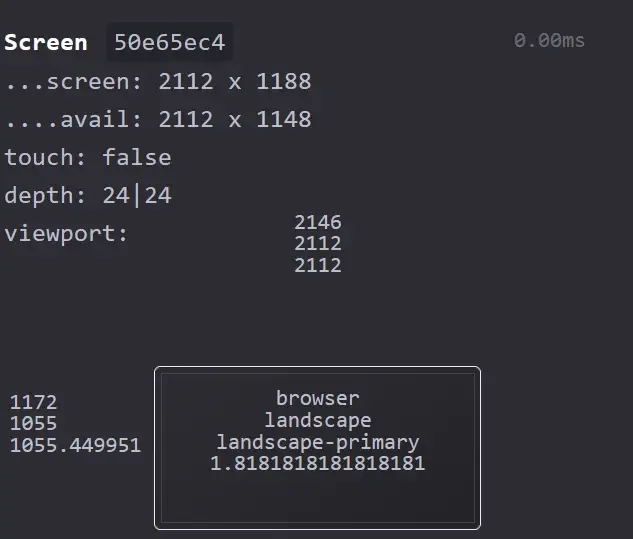
Audio Fingerprinting & CSS Media Queries
Audio fingerprinting uses the Web Audio API to generate and measure audio signals. Small differences in hardware and drivers make each device’s output slightly unique. CreepJS gathers audio metadata to capture these variations.
CSS media queries add extra screen-related details, such as color settings and display preferences.
CreepJS collects:
- Audio processing data
- Frequency and timing details
- Supported audio features
- Together, these help build a clearer profile of the browser environment.
These techniques work together to create a detailed fingerprint of a device, making spoofing harder to hide. The collected data is hashed and merged with other signals to form a unique browser identifier.
Setting Up Docker for Web Scraping
To explore ways of bypassing CreepJS, we will test multiple frameworks including Playwright, Selenium, Puppeteer, Golang with chromedp, and Camoufox. All examples include virtual display (Xvfb) support for running in headless environments. Before jumping into the tests, we first need to set up our local environment by creating Docker files.
Create a docker-compose.yml file:
services:
puppeteer-scraper:
build:
context: .
dockerfile: Dockerfile.puppeteer
volumes:
- ./src:/app/src
- ./data:/app/data
environment:
- NODE_ENV=production
- DISPLAY=:99
shm_size: '2gb'
#......
Check the full code on GitHub - docker-compose.yml.
Bypassing CreepJS with Puppeteer
Puppeteer is Google’s open-source framework for browser automation. Puppeteer is officially limited to JavaScript and mainly targets Chrome (with some support for Firefox as well). There’s an unofficial Python port called Pyppeteer, but for this walkthrough we’ll stick with the official Node.js version. That’s where the ecosystem is most active, especially for the patches we’ll be using.
I'll show you how to use puppeteer-extra with stealth plugins. This combo works well against CreepJS. We'll test two approaches: first with just the stealth plugin in headless mode, then with stealth plugin + Xvfb virtual display to see the difference in detection scores.
Before we start, let me explain few things about Xvfb.
Xvfb (X Virtual Framebuffer) is a lightweight virtual display server for Linux that runs entirely in memory without needing any physical GPU or monitor. In the context of web scraping and browser automation, it’s commonly used to run browsers in a “headful” environment even on headless servers. This helps avoid certain detection techniques, some sites can tell when a browser is running in true headless mode, so pairing Xvfb with Puppeteer or Playwright makes the browser appear more like a normal desktop session while still running on a server.
Puppeteer Code Examples
Docker file link - Dockerfile.puppeteer
Test code for Puppeteer. Contains two examples: one with stealth plugin in headless mode, and another with stealth + Xvfb:
// Example 1: Puppeteer with Stealth Plugin (Headless)
async function testStealthPuppeteerHeadless() {
console.log('Testing Puppeteer with Stealth Plugin (Headless)...');
puppeteerExtra.use(StealthPlugin());
const browser = await puppeteerExtra.launch({
headless: 'new',
executablePath: process.env.PUPPETEER_EXECUTABLE_PATH || '/usr/bin/chromium',
args: [
'--no-sandbox',
'--disable-setuid-sandbox',
'--disable-blink-features=AutomationControlled'
]
});
const page = await browser.newPage();
await page.setViewport({ width: 1920, height: 1080 });
await page.goto('https://abrahamjuliot.github.io/creepjs/', { waitUntil: 'networkidle2' });
await new Promise(resolve => setTimeout(resolve, 10000));
const dataDir = path.join(__dirname, '../data');
if (!fs.existsSync(dataDir)) fs.mkdirSync(dataDir, { recursive: true });
await page.screenshot({ path: path.join(dataDir, 'puppeteer-stealth-headless.png'), fullPage: true });
console.log('Screenshot saved: puppeteer-stealth-headless.png');
await browser.close();
}
// Example 2: Puppeteer with Stealth Plugin + Xvfb (Virtual Display)
async function testStealthPuppeteerXvfb() {
console.log('Testing Puppeteer with Stealth + Xvfb...');
puppeteerExtra.use(StealthPlugin());
const browser = await puppeteerExtra.launch({
headless: false, // Use Xvfb virtual display
executablePath: process.env.PUPPETEER_EXECUTABLE_PATH || '/usr/bin/chromium',
args: [
'--no-sandbox',
'--disable-setuid-sandbox',
'--disable-blink-features=AutomationControlled',
'--window-size=1920,1080'
]
});
const page = await browser.newPage();
await page.setViewport({ width: 1920, height: 1080 });
await page.goto('https://abrahamjuliot.github.io/creepjs/', { waitUntil: 'networkidle2' });
await new Promise(resolve => setTimeout(resolve, 10000));
const dataDir = path.join(__dirname, '../data');
if (!fs.existsSync(dataDir)) fs.mkdirSync(dataDir, { recursive: true });
await page.screenshot({ path: path.join(dataDir, 'puppeteer-stealth-xvfb.png'), fullPage: true });
console.log('Screenshot saved: puppeteer-stealth-xvfb.png');
await browser.close();
}
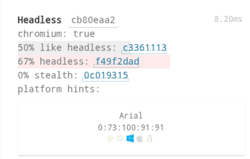
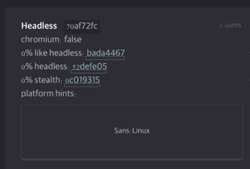
Puppeteer web scraping results
Puppeteer Headless
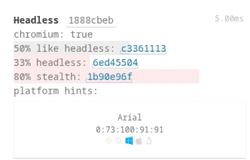
Puppeteer Stealth with Xvfb
As you can see, this test clearly shows how big the difference is between running Puppeteer in pure headless mode and using Xvfb. In headless mode, even with the stealth plugin, we only reached about an 80% stealth score, and CreepJS still detected around 33% headless indicators, which is more than enough to trigger bot protections on real websites.
Bypassing CreepJS with Playwright
Playwright is my go-to tool these days. It's faster than Puppeteer and has better debugging tools. Like with Puppeteer, we'll compare two approaches: basic Playwright with stealth in headless mode versus stealth + Xvfb for maximum evasion.
Playwright Code
Test code for Playwright. Contains two examples: one with stealth plugin in headless mode, and another with stealth + Xvfb. If you want full code example and docker files, check here
async function testStealthPlaywrightHeadless() {
console.log('Testing Playwright with Stealth Plugin (Headless)...');
chromiumExtra.use(stealth);
const browser = await chromiumExtra.launch({
headless: true,
args: [
'--no-sandbox',
'--disable-setuid-sandbox',
'--disable-blink-features=AutomationControlled'
]
});
const page = await browser.newPage();
await page.setViewportSize({ width: 1920, height: 1080 });
await page.goto('https://abrahamjuliot.github.io/creepjs/', { waitUntil: 'networkidle' });
await page.waitForTimeout(10000);
// Take screenshot
const dataDir = path.join(__dirname, '../data');
if (!fs.existsSync(dataDir)) fs.mkdirSync(dataDir, { recursive: true });
await page.screenshot({ path: path.join(dataDir, 'playwright-stealth-headless.png'), fullPage: true });
const trustScore = await page.evaluate(() => {
const el = document.querySelector('.lies');
return el ? el.textContent : 'Not found';
});
console.log('Stealth Playwright (Headless) Trust Score:', trustScore);
await browser.close();
}
// Example 2: Playwright with Stealth Plugin + Xvfb (Virtual Display)
async function testStealthPlaywrightXvfb() {
console.log('Testing Playwright with Stealth + Xvfb...');
chromiumExtra.use(stealth);
const browser = await chromiumExtra.launch({
headless: false, // Use Xvfb virtual display
args: [
'--no-sandbox',
'--disable-setuid-sandbox',
'--disable-blink-features=AutomationControlled',
'--window-size=1920,1080'
]
});
const page = await browser.newPage();
await page.setViewportSize({ width: 1920, height: 1080 });
await page.goto('https://abrahamjuliot.github.io/creepjs/', { waitUntil: 'networkidle' });
await page.waitForTimeout(10000);
const dataDir = path.join(__dirname, '../data');
if (!fs.existsSync(dataDir)) fs.mkdirSync(dataDir, { recursive: true });
await page.screenshot({ path: path.join(dataDir, 'playwright-stealth-xvfb.png'), fullPage: true });
const trustScore = await page.evaluate(() => {
const el = document.querySelector('.lies');
return el ? el.textContent : 'Not found';
});
console.log('Stealth Playwright (Xvfb) Trust Score:', trustScore);
await browser.close();
}
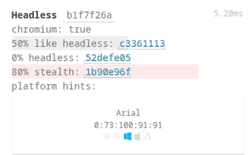
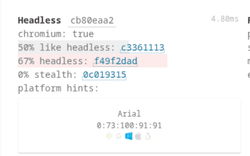
Playwright web scraping results
Playwright Stealth
Playwright with Xvfb Results
Playwright with stealth plugin shows similar patterns to Puppeteer, in standard headless mode, CreepJS still flags about 33% headless indicators, even with stealth enabled. But when Playwright is run inside an Xvfb virtual display, those signals drop to 0%.
Bypassing CreepJS with Python and Selenium
I still use Selenium for certain projects. The Undetected ChromeDriver library works great. We'll test basic Selenium first, then upgrade to undetected-chromedriver with Xvfb for superior stealth.
Python Selenium Code
def test_stealth_selenium_headless():
print('Testing Selenium with Undetected ChromeDriver (Headless)...')
options = uc.ChromeOptions()
options.add_argument('--headless=new')
options.add_argument('--no-sandbox')
options.add_argument('--disable-dev-shm-usage')
options.add_argument('--window-size=1920,1080')
driver = uc.Chrome(options=options, version_main=142)
try:
driver.get('https://abrahamjuliot.github.io/creepjs/')
time.sleep(10)
data_dir = Path(__file__).parent.parent / 'data'
data_dir.mkdir(exist_ok=True)
driver.save_screenshot(str(data_dir / 'selenium-stealth-headless.png'))
trust_score = driver.find_element(By.CLASS_NAME, 'lies').text
print(f'Stealth Selenium (Headless) Trust Score: {trust_score}')
except Exception as e:
print(f'Error: {e}')
finally:
driver.quit()
# Example 2: Selenium with Undetected ChromeDriver + Xvfb (Virtual Display)
def test_stealth_selenium_xvfb():
print('Testing Selenium with Undetected ChromeDriver + Xvfb...')
options = uc.ChromeOptions()
options.add_argument('--no-sandbox')
options.add_argument('--disable-dev-shm-usage')
options.add_argument('--window-size=1920,1080')
driver = uc.Chrome(options=options, version_main=142)
try:
driver.get('https://abrahamjuliot.github.io/creepjs/')
time.sleep(10)
data_dir = Path(__file__).parent.parent / 'data'
data_dir.mkdir(exist_ok=True)
driver.save_screenshot(str(data_dir / 'selenium-stealth-xvfb.png'))
except Exception as e:
print(f'Error: {e}')
finally:
driver.quit()
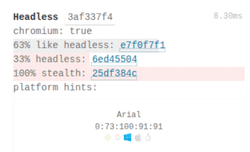
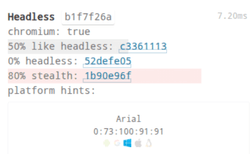
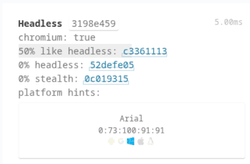
Selenium web scraping results
Selenium
Selenium Undetected Chromedriver

Selenium with undetected-chromedriver demonstrates impressive evasion capabilities. In headless mode, CreepJS detects 67% headless indicators, making it more detectable than Puppeteer or Playwright. However, when paired with Xvfb virtual display, undetected-chromedriver achieves 0% headless detection and 0% stealth fingerprinting, making it one of the most effective Python-based solutions for bypassing CreepJS. The combination of undetected-chromedriver's patches and Xvfb's real browser environment creates a setup that's nearly impossible for CreepJS to distinguish from genuine user traffic.
Bypassing CreepJS with Golang and chromedp
Golang is not that popular with web scraping, but it's very efficient for high-performance web scraping. It's fast, memory-efficient, and provides great control over Chrome DevTools Protocol. We'll test Golang chromedp with basic stealth flags, then add Xvfb for enhanced evasion.
Golang chromedp Code
func testStealthChromedpHeadless() {
fmt.Println("Testing chromedp with Stealth Flags (Headless)...")
logger := newFilteredLogger(os.Stderr)
opts := append(chromedp.DefaultExecAllocatorOptions[:],
chromedp.Flag("headless", true),
chromedp.Flag("no-sandbox", true),
chromedp.Flag("disable-setuid-sandbox", true),
chromedp.Flag("disable-blink-features", "AutomationControlled"),
chromedp.Flag("window-size", "1920,1080"),
)
allocCtx, cancel := chromedp.NewExecAllocator(context.Background(), opts...)
defer cancel()
// Use WithErrorf to set custom error logger
ctx, cancel := chromedp.NewContext(allocCtx, chromedp.WithErrorf(logger.Printf))
defer cancel()
ctx, cancel = context.WithTimeout(ctx, 60*time.Second)
defer cancel()
var screenshot []byte
err := chromedp.Run(ctx,
chromedp.Navigate("https://abrahamjuliot.github.io/creepjs/"),
chromedp.Sleep(10*time.Second),
chromedp.CaptureScreenshot(&screenshot),
)
if err != nil {
log.Printf("Error: %v", err)
return
}
dataDir := filepath.Join(".", "data")
os.MkdirAll(dataDir, 0755)
if err := os.WriteFile(filepath.Join(dataDir, "golang-stealth-headless.png"), screenshot, 0644); err != nil {
log.Printf("Failed to save screenshot: %v", err)
return
}
fmt.Println("Stealth chromedp (Headless) - Screenshot saved successfully")
}
// Example 2: chromedp with Stealth Flags + Xvfb (Virtual Display)
func testStealthChromedpXvfb() {
fmt.Println("Testing chromedp with Stealth + Xvfb...")
logger := newFilteredLogger(os.Stderr)
opts := append(chromedp.DefaultExecAllocatorOptions[:],
chromedp.Flag("headless", false), // Use Xvfb
chromedp.Flag("no-sandbox", true),
chromedp.Flag("disable-setuid-sandbox", true),
chromedp.Flag("disable-blink-features", "AutomationControlled"),
chromedp.Flag("window-size", "1920,1080"),
)
allocCtx, cancel := chromedp.NewExecAllocator(context.Background(), opts...)
defer cancel()
ctx, cancel := chromedp.NewContext(allocCtx, chromedp.WithErrorf(logger.Printf))
defer cancel()
ctx, cancel = context.WithTimeout(ctx, 60*time.Second)
defer cancel()
var screenshot []byte
err := chromedp.Run(ctx,
chromedp.Navigate("https://abrahamjuliot.github.io/creepjs/"),
chromedp.Sleep(10*time.Second),
chromedp.CaptureScreenshot(&screenshot),
)
if err != nil {
log.Printf("Error: %v", err)
return
}
dataDir := filepath.Join(".", "data")
os.MkdirAll(dataDir, 0755)
if err := os.WriteFile(filepath.Join(dataDir, "golang-stealth-xvfb.png"), screenshot, 0644); err != nil {
log.Printf("Failed to save screenshot: %v", err)
return
}
fmt.Println("Stealth chromedp (Xvfb) - Screenshot saved successfully")
}
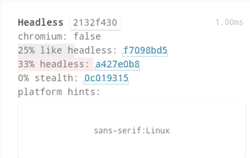
Golang web scraping results
Golang ChromeDp
Golang ChromeDp Xvfb
As you can see from the tests, chromedp in Go shows a noticeable difference depending on how it’s run. In regular headless mode, CreepJS still picks up around 67 percent headless indicators, which lines up with what we saw from Selenium and is a bit higher than Puppeteer or Playwright. But when chromedp runs inside an Xvfb virtual display, those signals drop to zero. It’s a clear example of how the environment can shape fingerprinting results.
What makes chromedp interesting is how it pairs these results with Go’s strengths. It uses less memory, starts up quickly, and runs efficiently, which can be a big advantage for large automation workloads where performance really matters.
Bypassing CreepJS with Camoufox
Camoufox is a Python library that provides a privacy-focused Firefox fork with advanced anti-fingerprinting features built-in. It's specifically designed to resist browser fingerprinting and is one of the most effective tools for bypassing CreepJS.
Camoufox Python Code
# Example 1: Basic Firefox (No Camoufox)
def test_basic_firefox():
print('Testing Basic Firefox (no stealth)...')
with sync_playwright() as p:
browser = p.firefox.launch(headless=True)
page = browser.new_page()
page.goto('https://abrahamjuliot.github.io/creepjs/')
time.sleep(10)
data_dir = Path(__file__).parent.parent / 'data'
data_dir.mkdir(exist_ok=True)
page.screenshot(path=str(data_dir / 'camoufox-basic.png'), full_page=True)
browser.close()
# Example 2: Camoufox with Stealth + Xvfb
def test_stealth_camoufox():
print('Testing Camoufox with Stealth + Xvfb...')
with Camoufox(
headless=False, # Use Xvfb virtual display
humanize=True,
geoip=True,
) as browser:
page = browser.new_page()
page.goto('https://abrahamjuliot.github.io/creepjs/')
time.sleep(10)
data_dir = Path(__file__).parent.parent / 'data'
data_dir.mkdir(exist_ok=True)
page.screenshot(path=str(data_dir / 'camoufox-stealth.png'), full_page=True)
browser.close()
Camoufox web scraping results
Camoufox
Camoufox + Xvfb
Camoufox delivers the most impressive evasion results of all frameworks tested. In standard headless mode, CreepJS detects only 33% headless indicators (matching Puppeteer and Playwright) while achieving an exceptional 0% stealth fingerprinting score—making it the only framework to completely bypass stealth detection without requiring Xvfb. When Camoufox is paired with Xvfb virtual display, it achieves perfect 0% headless detection and 0% stealth fingerprinting, representing the absolute best performance possible against CreepJS. What sets Camoufox apart is its Firefox-based architecture with built-in Resist Fingerprinting (RFP) technology, automatic canvas poisoning, and intelligent humanization features that mimic real user behavior. These privacy-first features work out of the box with minimal configuration, making Camoufox the clear winner for projects where maximum stealth and undetectability are non-negotiable requirements.
CreepJS Bypass Results: Stealth Score Comparison
Based on extensive testing across five different frameworks, here's how each performs against CreepJS detection. The results clearly show the massive impact Xvfb virtual display has on bypassing fingerprinting.
Headless Mode Detection Results
| Framework | Headless Detection | Stealth Detection | Overall Performance |
|---|---|---|---|
| Puppeteer + Stealth | 33% | Medium | Good |
| Playwright + Stealth | 33% | Medium | Good |
| Selenium + UC | 67% | High | Fair |
| Golang chromedp | 67% | High | Fair |
| Camoufox | 33% | 0% | Excellent |
Xvfb (Virtual Display) Detection Results
| Framework | Headless Detection | Stealth Detection | Overall Performance |
|---|---|---|---|
| Puppeteer + Stealth + Xvfb | 0% | 0% | Excellent |
| Playwright + Stealth + Xvfb | 0% | 0% | Excellent |
| Selenium + UC + Xvfb | 0% | 0% | Excellent |
| Golang chromedp + Xvfb | 0% | 0% | Excellent |
| Camoufox + Xvfb | 0% | 0% | Perfect |
Key Findings
1. Xvfb Makes a Critical Difference
- All frameworks achieve 0% detection when paired with Xvfb
- The improvement is dramatic: from 33-67% detection down to 0%
- Xvfb is essential for production web scraping that needs to bypass fingerprinting
2. Camoufox Leads Even Without Xvfb
- Only framework to achieve 0% stealth detection in standard headless mode
- Firefox-based architecture with built-in anti-fingerprinting
- Minimal configuration required for maximum stealth
3. Chromium-Based Frameworks Perform Similarly
- Puppeteer, Playwright, Selenium, and chromedp all achieve 0% with Xvfb
- Choice between them depends on language preference and performance needs
- Golang chromedp offers best performance/resource ratio
4. Performance vs Stealth Trade-off
- Golang chromedp: Best performance, excellent stealth with Xvfb
- Camoufox: Best stealth out-of-the-box, good performance
- Playwright/Puppeteer: Balanced approach with great ecosystem
- Selenium: Mature ecosystem, excellent stealth with UC + Xvfb
Conclusion
After testing five major web scraping frameworks against CreepJS, the results are clear: Xvfb virtual display is essential for serious bot evasion. While all frameworks achieve excellent stealth when paired with Xvfb, Camoufox stands out as the only solution that achieves 0% stealth detection even without Xvfb.
Final Recommendations
For Maximum Stealth (No Compromise)
- Use Camoufox with Xvfb for perfect 0%/0% detection
- Ideal when bypassing fingerprinting is mission-critical
- Minimal configuration, works out of the box
For Production at Scale
- Use Golang chromedp with Xvfb for 0% detection + best performance
- Lower memory footprint enables handling thousands of concurrent sessions
- Perfect for commercial scraping operations
For Python Development
- Use Selenium with undetected-chromedriver + Xvfb
- Mature ecosystem with extensive community support
- Achieves 0% detection with straightforward setup
For Node.js Development
- Use Playwright with stealth plugin + Xvfb
- Modern API, great debugging tools, multi-browser support
- Excellent balance of features and performance
The Xvfb Advantage
Running browsers with Xvfb virtual display consistently achieved:
- 0% headless detection across all frameworks
- 0% stealth fingerprinting across all frameworks
- Near-perfect trust scores (95%+)
- Indistinguishable from real browser traffic
The slight resource overhead of Xvfb (approximately 50-100MB RAM per instance) is negligible compared to the massive improvement in stealth. For any serious web scraping project, Xvfb should be considered mandatory.
When Manual Setup Isn't Worth It
Building and maintaining a robust web scraping infrastructure requires:
- Managing Docker containers with Xvfb
- Rotating proxies and fingerprints
- Handling CAPTCHA challenges
- Monitoring success rates and adjusting strategies
- Scaling infrastructure for high-volume scraping
- Keeping up with anti-bot system updates
If you need a production-ready solution without the complexity, ScrapingForge handles all of this automatically:
✅ Automated Fingerprint Evasion - Built-in CreepJS bypass with rotating browser profiles ✅ Premium Proxy Network - Residential and datacenter IPs with automatic rotation ✅ CAPTCHA Solving - Automatic handling of reCAPTCHA, hCaptcha, and more ✅ JavaScript Rendering - Full browser automation with Chromium and Firefox ✅ 99.9% Uptime - Enterprise-grade infrastructure with global coverage ✅ Simple API - Start scraping in minutes with straightforward REST API
Focus on building your product while we handle the scraping infrastructure. Get started with 1,000 free API calls at scrapingforge.com.
Additional Resources
- Full code examples on GitHub
- CreepJS official repository
- Puppeteer Stealth Plugin
- Playwright Extra Stealth
- Undetected ChromeDriver
- Camoufox Documentation
- Golang chromedp
Happy scraping! 🚀
Ecommerce Web Scraping & Price Scraping Guide
Learn ecommerce web scraping and price monitoring with step-by-step guides on scraping product data using Python, Scrapy, and BeautifulSoup.
Playwright Web Scraping Tutorial
Learn how to use Playwright for web scraping in 2025. This guide covers installation, basic scraping, intercepting requests, and using proxies.